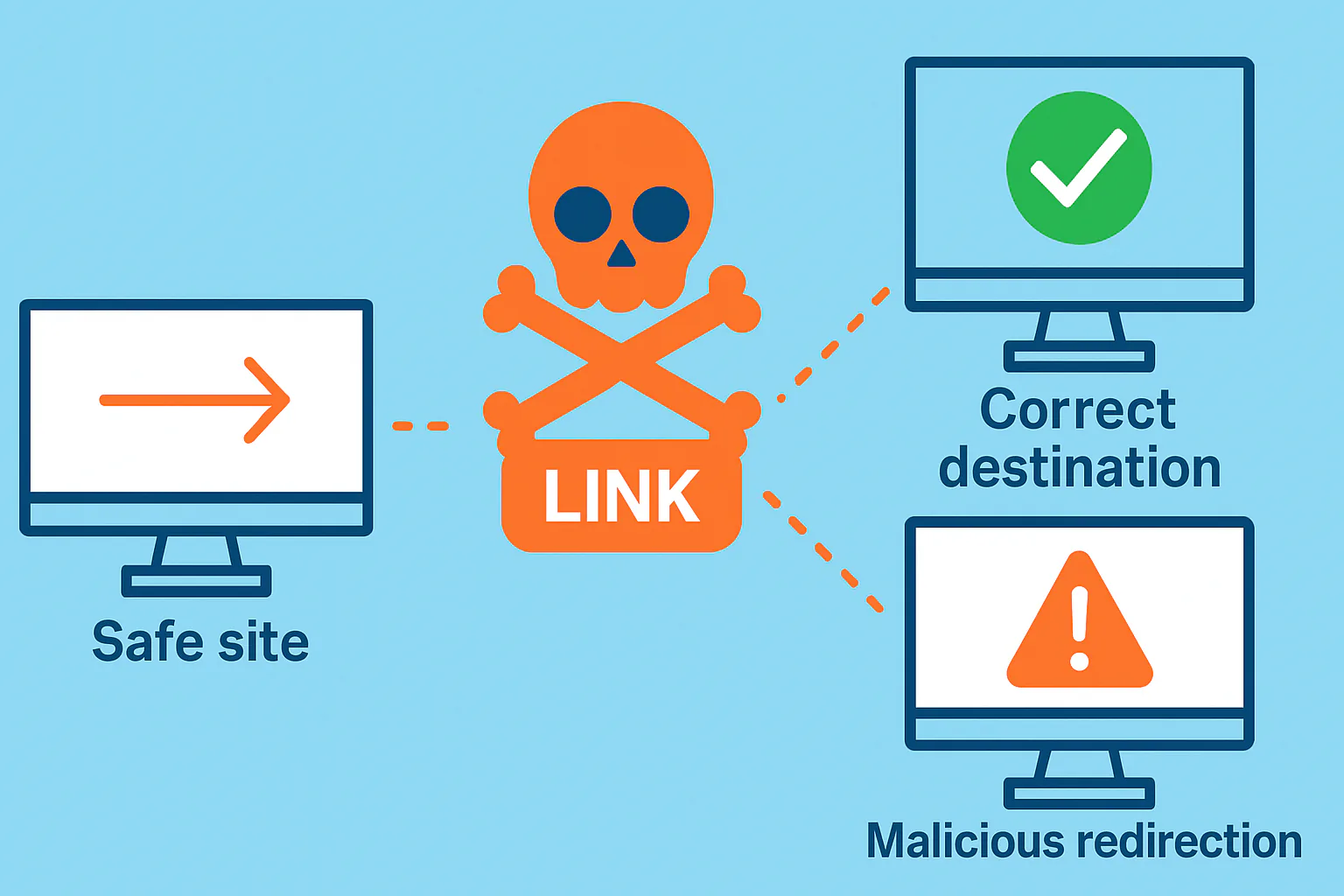
Sarah clicks her local florist’s homepage to order flowers. Instead of petals, she lands on a knockoff “Amazon Flash Sale” demanding her card number. Her data vanishes—stolen by a redirect you never saw coming.
This isn’t bad luck; it’s the new normal. In 2025, malicious redirects surged 42%, silently rerouting small-business traffic to fake shops and malware traps. Hackers aren’t just breaching sites—they’re hijacking your hard-earned traffic, monetizing trust and SEO equity for scam profits while your analytics show “normal” bounces.
For small businesses, where every click counts, these invisible detours erode loyalty and can even trigger browser blacklists. With malvertising up sharply in 2025, a single compromised script can turn your traffic into a hacker’s revenue stream overnight.
The 2025 Redirect Rampage: From Nuisance to Epidemic
Once an annoyance of shady pop-ups, redirects have evolved into AI-tuned, seamless traps that evade browsers and antivirus tools. This year, forced redirects dominated malvertising campaigns, driving a 47% YoY surge in cyberattacks on small businesses.
WordPress sites—powering 43% of the web—took the hardest hits. Attacks now strike every 32 minutes, with website compromises accounting for 15% of SMB incidents, often through injected redirect code. Phishing emails amplify the threat, as malicious URLs quadrupled in campaigns leading victims straight to infected hosts.
-
Scam Stores: Traffic funneled to fake e-commerce sites pushing “flash deals” that drain credit cards—over $2.5 billion in losses in the first half of 2025 alone.
-
Malware Drops: Drive-by downloads silently install trojans and botnets.
-
Affiliate Grifts: Hackers earn shady commissions, cashing in on your visitors’ clicks.
Small sites suffer most—because they rarely see it coming.
The Hijack Unraveled: A Day in the Life of a Compromised Click
It plays out like a digital heist—subtle, automated, and nearly invisible.
Incident Log — Timeline of a Redirect Hijack
[08:12:03] INBOUND EMAIL → "Plugin Update Available" [08:12:47] ADMIN ACTION → Link clicked — authentication spoofed [12:47:11] PAYLOAD INJECTED → /themes/footer.php [15:09:05] REDIRECT TRIGGERED → 302 → fake-shopify-checkout.com [15:09:10] TRACKER LOGGED → Affiliate ID #7284
Behind the scenes, the attacker’s affiliate tracker logs the event, pocketing pennies per victim while malware installs silently. By nightfall, the code has rewritten itself through a botnet update.
Most owners don’t notice until angry emails arrive—and by then, 57% of SMBs have already lost control of at least part of their traffic pipeline.
Collateral Damage: When Redirects Reroute Your Entire Business
One rogue redirect can ripple through your entire operation.
Lost Trust = Lost Traffic
Visitors blame you for the scam. Over 70% never return after a malicious redirect experience—causing 20–30% traffic dips in weeks.
Blacklisted Overnight
Google and major browsers flag your domain. Your rankings tank, your emails bounce, and recovery can take months—even after the infection’s gone.
Legal Fines and PR Fallout
If malware spreads from your domain, regulators may classify it as a data breach. In 2025, average SMB breach costs hit $1.6 million, combining cleanup, downtime, and reputation repair.
| Redirect Type | Tactic Twist | 2025 Toll |
|---|---|---|
| Scam Stores | Affiliate-fueled fakes | $2.5 B fraud from traffic funnels |
| Malware Drops | Drive-by infections | 15% of SMB hacks via sites |
| Phishing Pivots | URL-masked lures | Malicious links × 4 in email threats |
Lock It Down: Protection That Pays for Itself
You don’t need a Fortune 500 budget to stop Fortune 500-grade attacks.
Our managed website security service automates patching, scanning, and real-time monitoring—detecting malicious redirects and injected scripts before they hijack your audience.
Your traffic isn’t just data—it’s dollars at stake. Redirect the risk back to the hackers.
Take Control: Scan Your Site Today
Spot redirects before they spot your visitors.
Our free traffic hijack detector crawls for suspicious scripts, URL anomalies, and scam signals—in minutes, with easy fixes.
Sources: Stats sourced from StrongDM Small Business Cybersecurity, Heimdal Security SMB Stats, Bennett/Porter Threat Landscape, NinjaOne SMB Stats, Cyber Defense Magazine Malvertising, Melapress WP Security, Hostinger WP Stats, and AdMonsters Malvertising Report. For full details, visit the linked reports.
Related Reading
-
Your Small Site: The Unwitting Host for 2025's Fake Amazon Phishing Boom
Phishing scams are thriving on hacked small business sites — learn how yours could be next. -
The Rise of Automated Attacks: Why Small Businesses Are Prime Targets
Automated bots relentlessly probe small sites, planting redirects and backdoors unnoticed. -
AI Is Supercharging Hackers — Here's Why Your Website Is at Risk
AI-driven scripts now power the mass redirect campaigns draining small site traffic and trust.